With comments and summary from Ray Demeo
Key Takeaways for Executives*
• The government shutdown made it harder for contractors to attract and retain top talent.
• The tight labor market worsens this effect, as employees have more options for jumping ship than they had during previous shutdowns.
• Larger firms were able to switch employees to other contracts that still have funding or pay them to take additional training, but these stop-gap measures didn’t work for smaller firms.
*Washington Exec
The Shutdown Hurt Contractor Staff Recruiting, Retention
The government shutdown may have ended but many side effects remain. This article highlights two of them. The first is the affect the shutdown is having and will continue to have on contractor staff and employee personnel. When it comes to hiring good talent, the government has always faced steep competition with private employers, for both contractors and employees. Private organizations can often pay high salaries but government employers could counter that with stability, pensions and other benefits. But now, with three shutdowns in 2018 alone, government cybersecurity jobs are looking far from appealing on any level.
Some larger companies were able to shift contractors to a different, funded department but small firms didn’t have those options. Even after this shutdown and back pay is received, as has happened before, many employees may choose to leave and avoid having to face this kind of situation again. The current tight labor market gives employees more options of places to go.
Ray DeMeo, co-founder and chief operating officer at Virsec, told WashingtonExec it’s hard for a company to recruit people to work on contracts whose government counterparts — contracting officers, etc. — are currently furloughed. And he noted many firms don’t have much financial flexibility. “Contractors bid these jobs as tight as they can and work very hard to recruit, DeMeo said. “Not every contractor has huge operational overhead to retain people.”
He also agreed the shutdown is threatening to take the sheen off government contract work.
“It makes those jobs less stable than other jobs in the commercial sector,” DeMeo said. “And if a government contractor employee feels like a job is less stable or less fulfilling, it’s a no brainer to take another opportunity.”
Government shutdown laid out a “welcome mat” for hackers
Another critical front – cybersecurity -- received little attention until last week but it also is in a sober state thanks to the shutdown. In some ways, the staffing concerns overlap with the worries about cyber security. Reports said cyber security threats skyrocketed during the shutdown. Even when the US government is fully staffed and “on it,” cyber threats persist on a moment-by-moment basis.
A news report during the shutdown described the parking lot at the Department of Homeland Security (DHS) as being nearly empty. In a shutdown where only non-essential parts of the government were supposed to be closed, it begs the question of what criteria makes something essential or not.
“According to the MIT Technology Review, approximately 45 percent of employees at the Cybersecurity and Infrastructure Protection Agency(a part of DHS), and 85 percent of staffers at the National Institute of Standards and Technology (NIST), were on furlough.”
While the DHS and other agencies are side-lined, ill-intentioned nation states and attackers who have repeatedly targeted us in the past (Russia, China, North Korea, Iran) see this as an open door to take advantage of until we get our act together. They already have activities in motion and this provides a supreme opportunity to hit the accelerator. We may not see effects right away. Often what we have seen from these nation states is missions of reconnaissance, including invasions of US electric grids and utilities (see recent articles)*. But those invasions are widely viewed as preliminary nefarious steps to possible takeovers or shutdowns.
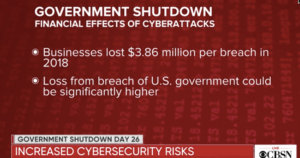
Significant breaches are also a threat. They happened before and they rack up costs on multiple fronts, including monetary. The cost of breaches to corporations on average is $4 million. The cost to the government for breaches is far more. In its shutdown considerations, or lack thereof, the government didn’t factor in that a data breach that would target itself during a shutdown could cost taxpayers millions. And without regular staff on duty for weeks as the shutdown dragged on, future damages could be far worse.
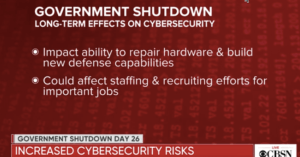
Ray DeMeo points out how the staffing problem and the cybersecurity problem are tied together, saying the government shutdown could have negative long-term consequences on government staffing and recruiting for important cybersecurity jobs in the future. These jobs, DeMeo says, keep Americans safe.
Has the US government been shown to be vulnerable before?
Sometime in the summer of 2016, a group called The Shadow Brokers broke into The Equation Group, a division within the government’s National Security Agency (NSA), and stole the largest treasure trove of sophisticated hacking tools (Double Pulsar, Eternal Blue behind WannaCry, Not Petya, etc.), the world has ever seen. Since then, repeated cyber attacks using those tools have continued to plague organizations around the globe. That theft happened with our government fully staffed, open and up and running. What might bad actors have done while no one was at the wheel for weeks on end?
Summary from Virsec’s Ray DeMeo:
Bottom line - the shutdown's impact to national security
Government employees who cannot pay their rent, mortgage or daycare as a result of the shutdown are going to think twice about putting their families in this position again. The decision is made much easier by the reality that there are tens of thousands of unfilled job openings in the private sector waiting for candidates. As for recruiting newcomers to the ranks of government data center security and SOC environments, the public-private pay gap makes it hard enough to attract talent as it is.
The long-term damage being done to our nation's cyber security workforce as a result of the government shutdown is unconscionable.
When it comes to cyber security, we need our government operating at 100%, running full speed. In a non-shutdown environment, demand for government data center cyber security analysts and incident responders is at an all-time high. Even at full-capacity, resources are at a bare minimum for the mountain of work at hand, just to get the government's IT infrastructure up to minimum levels of resiliency, all while working against the nonstop firehose of hour-by-hour attacker assaults.
Attempting to parse critical and non-critical cyber personnel is not possible - it's quite literally dismissing the people who are building your fort while you are in the middle of fighting a war.
As noted above, 45% of employee at the Cybersecurity and Infrastructure Protection Agency, and at 85% of the staff at NIST were furloughed for 4 weeks. During that time, NIST's critical cyber standards not accessible on its website.
The furlough of government cyber talent will have morale, retention and recruiting effects well after a shutdown ends. A drop in cyber talent was notable following the government shutdown in 2013 as high-value personnel left for better paying more stable environments.
In any organization, teamwork erodes, lines of communication are lost, action plans and key milestones fall apart. Recovery time will be much longer than the duration of the shutdown itself.
Read full Shutdown starting to hurt contractor staff and Government shutdown lays out hacker “welcome mat”articles
Recent articles about Russia attacking US electric grids:
1. Despite US defenses, Russian hackers are still trying to break in to America’s power grid
2. Could Russia Shut Down US Electric Grids?
3. DHS gives more details, including unclassified info, about electrical grid attacks by Russian agents
4. Russian Hackers Breach US Utility Networks via Trusted Vendors
5. US-CERT Finds Russian Hackers Spent Months Inside Targeted Systems