TechNewsWorld, January 10, 2020, with comments by Willy Leichter;
Ransomware danger tops the list of cybersecurity threats for 2020.
Ransomware is successful because, well, it’s successful. Enough victims cave to the demands to make it worth the attacker’s continued efforts. The more victims they find, the more money they extort and we're watching the cycle of ransomware danger ratcheting up and up. For the hackers, they’ve found a money tree so why not keep picking the fruit?
Authorities like DHS and the FBI discourage companies from paying these extorters and many do refrain. But some also feel compelled to pay out of desperation to get their data back. If they don’t have a clean backup handy, the fastest option to getting back to normal is paying the ransom, despite all the downsides of doing so.
Last year, 2019, was the worst year for ransomware on record. By one set of statistics, ransomware occurrences were up 18% in 2019, over the usual 12% year over year. Ransomware represented 40% of claims from manufacturers and 23% of smaller businesses. Ransomware is drawing cyberthieves faster than ever before, and certain industries are in the cross hairs more than others. These thieves are anything but bashful – they continue to conduct increasingly bold tactics in their attacks and in their demands.
Why Success Is Easy
Many ransomware attacks would not be successful if users would either be better trained or remember their training versus clicking on an unproven link without thinking. Trust is assumed too easily in the spur of the moment when users see what they think is a familiar sender of an email. Or, they quickly go to potentially unknown websites or open email attachments without vetting the source. These days, not every email is actually from the sender it says it’s from and it can take critical thinking to spot the queues that something’s not right. Being too quick to pull the “click trigger” can result in massive damage.
Ransomware doesn’t discriminate – bad actors have favorite industries they love to target – such as, city and municipal governments, schools, healthcare, financial institutions, critical infrastructure, manufacturing, high tech and individual businesses. In 2019 attacks, many victims in these industries had their computerized processes brought to a complete halt.
As noted above, security agencies apply pressure against paying the ransomware. In cities that experienced attacks, over 225 US mayors pledged together that they would not pay hackers and they backed it up by signing a resolution to that effect. But not every attacked business can stake that claim.
Going from Bad to Horrendous
It’s bad enough to be blocked from your data by having hackers encrypt it our from under you. But in 2019 rans-hackers upped the ante by threatening to publish the data they accessed if the ransom wasn’t paid, along with other extortionist threats to coerce payment. These creative threats heighten the stress, as intended.
"Once attackers have a foothold, it's easier for them to encrypt data for ransom than to exfiltrate data to sell on the dark Web," notes Willy Leichter, vice president at Virsec. "Cryptocurrencies now make it easy for criminals to monetize attacks anonymously. Recent attacks have encrypted data and threatened to expose it publicly if the victim doesn't pay up. While this is possibly a bluff, it raises the perceived stakes for victims, increasing their desperation and willingness to pay."
When companies find themselves under this kind of pressure, they sometimes pay the required ransom, and often they do get their data back. It happens enough that for some, a budget is set aside for just this circumstance should it arise and it’s considered a cost of doing business. Painful, but maybe less so than having their business rendered inoperable for however long. (It’s worth noting that cyberinsurance policies can include covering ransomware costs, and sometimes paying it can nullify a policy.)
The Worst Ransom-Mare of All
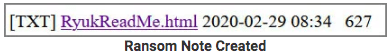
The ransomware nightmare has escalated with recent malware and when that happens, there’s no waking up from the scenario if it strikes your company. What’s worse than having your data encrypted and being blocked from accessing it unless you pay ransom to get it back? Having the data-nappers wipe it out completely so that it can never be retrieved.
The cyber-criminals commit the first crime - datanapping - and then they commit data-cide by wiping it all out. These wiper attacks include not just the data but the entire network and system so that it’s permanently unrecoverable. The danger of ransomware is already high enough, but this is every organization’s biggest nightmare.
If this happens, even backups are unlikely to work because they are probably infected as well. Any attempt at restoring also becomes corrupt. Experts believe wiper worms are among the top cyberthreats companies face this year.
Unrealistic Self Perception When It Comes to Preparedness
According to Forrester, businesses think they have greater level of preparedness for a cyberattack and what’s required for recovery than they actually have. Of the companies who said they feel confident in their preparations (77%), well under a third of them actually had a contingency plan (21%). And only half of those (11%) believed they could recover in three days or less. That kind of inaccurate self-evaluation only makes the threat worse.
Maybe a different kind of statistic will open some eyes to the reality of the problem: When NotPetya hit the shipping giant Maersk and encrypted 55,000 of its servers, along with numerous other organizations' devices around the world, it took only 7 minutes.
Read full Cybersecurity 2020: The Danger of Ransomware article.
Further resources:
Solution briefs:
Solution Brief: Protection Against Advanced Web Attacks
The Ransomware Epidemic – 1-page Solution Brief
Demos:
Demo: Multi-Level Protection Against Ransomware
Articles:
Prepare for Cyber Attacks from Iran, Especially 'Wiper' Attacks
MegaCortex Ransomware Worsens — Hackers Change Users’ Passwords & Make Blackmail Demands
Ransomware Attack: Cybercriminals Hit California School District
It’s October, Cybersecurity Awareness Month, & Ransomware Is the Biggest Fight We’re Losing
LockerGoga Ransomware Slams Industrial Firms in Europe with Devastating Impact